Fireball: Browser Hijacker/Adware
Original Issue Date:-
June 02, 2017
Type:-
Adware
Severity:-
Low
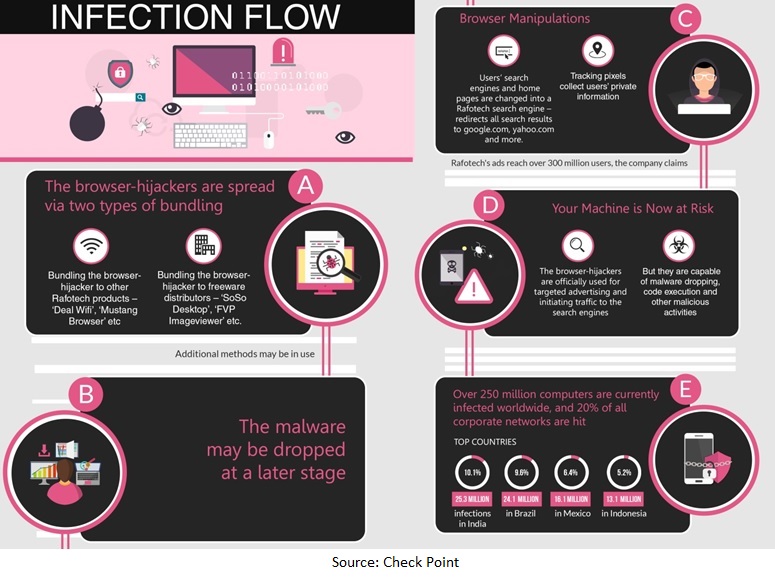
It has been reported that a malware named as "Fireball" targeting browsers is spreading worldwide. The malware "Fireball" has the ability to collect user information, manipulating web-traffic to generate ad-revenue, malware dropping and executing malicious code on the infected machines. According to the reports, Fireball currently installs plug-ins and additional configurations to boost its advertisements, but it could be used as distributor for any additional malware in future.
This malware is detected by majority of the antivirus solutions, users are advised to install and maintained updated antivirus solution to protect their computers from this malware infection.
Aliases:
Ad-Aware:-(Gen:Variant.Johnnie, Gen:Variant.Symmi, Gen:Variant.Zusy, Gen:Variant.Mikey)
AegisLab:-(Troj.Generickd!c, Gen.Variant.Zusy!c, Adware.W32.Elex!c
AhnLab-V3:-(PUP/Win32.ELEX)
ALYac:-(Gen:Variant.Johnnie)
Arcabit:-(Trojan.Johnnie, Trojan.Symmi, Trojan.Zusy, Trojan.Mikey, Trojan.Adware.Graftor, Adware.Generic)
Avast:-(Win32:Adware-gen [Adw])
AVG:-(Generic7.BSRM, Elex.APU)
Avira (no cloud):-(ADWARE/Adware.Gen7)
CAT-QuickHeal:-(Pua.Elex)
Comodo:-(Application.Win32.BrowseFox.qqtbw)
ESET-NOD32:-(a variant of Win32/Adware.ELEX.AD)
Fortinet:-(Riskware/Elex)
F-Secure:-(Gen:Variant.Adware.Graftor, Gen:Variant.Adware.Zusy, Adware:W32/Elex)
K7AntiVirus:-(Adware)
K7AntiVirus:-(Riskware)
Kaspersky:-(not-a-virus:AdWare.Win32.ELEX.ads)
Kaspersky:-(HEUR:Trojan.Win32.Generic
McAfee:-(RDN/Generic PUP.x, Artemis!84DCB96BDD84, Win32.Generic.cm, Win32.Dropper, Win32.Downloader)
Panda:-(Trj/GdSda.A)
Sophos:-(Generic PUA AD)
TrendMicro:-(TROJ_GEN.R002C0EAT17)
Webroot:-(W32.Adware.Gen)
Yandex:-(PUA.Agent!)
Yandex:-(PUA.ELEX!)
It is reported that the malware “Fireball” is used by one of the largest marketing agency to manipulate the victims’ browsers and changes their default search engines and home-pages into fake search engines. It also redirects the queries to either yahoo.com or Google.com. The fake search engines also collects the users’ private information.
Fireball is capable of performing following tasks:
- Acts as a browser-hijacker
- manipulating web-traffic to generate ad-revenue
- Capable of downloading further malware
- Capable of executing any malicious code on the victim machine
- Collects user information & steal credentials from victim machine
Installations:
Fireball is spreading via bundling, it gets installed on victim machines alongside other freeware programs, mostly without user’s consents. Popular vectors of spreading Fireball are bundling the malware to other products such as “Deal Wifi” and “Mustang Browser” or bundling via other freeware distributors/products such as “Soso Desktop”, “FVP Imageviewer” etc.
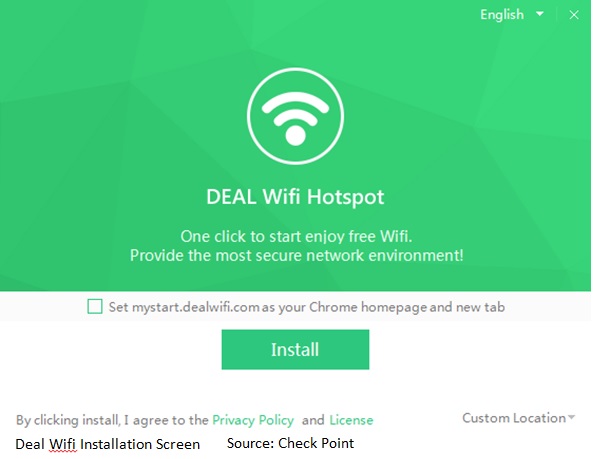
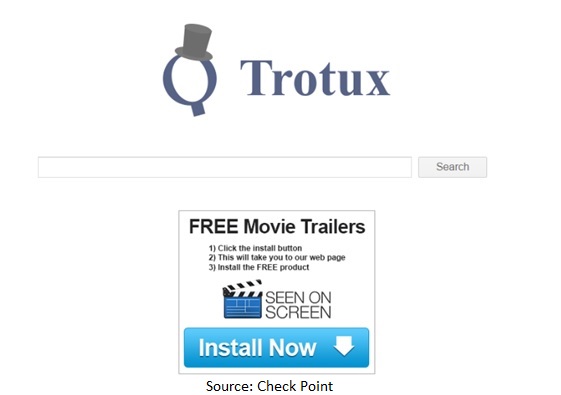
Upon installation, malware manipulates the victims’ browsers, it changes the default search engines and home-pages into fake search engines. It acts as a browser-hijacker, manipulates infected users’ web-traffic to generate ad-revenue. The fake search engine opened on victim’s infected web browser is shown below.
How to determine the infection
Open the web browser on your computer and try to:
- The home page is set by you or not?
- Are you able to modify the homepage?
- What is the default search engine? Are you able to change the default search engine?
- Check for the browser plug-in installed, some extra plugins installed by you?
If the answers to above questions is "NO", you might be a victim of Adware, it is requested to kindly scan your machine with updated antivirus.
Indicators of compromise (IoC)
Command & Control addresses:
attirerpage[.]com
s2s[.]rafotech[.]com
trotux[.]com
startpageing123[.]com
funcionapage[.]com
universalsearches[.]com
thewebanswers[.]com
nicesearches[.]com
youndoo[.]com
giqepofa[.]com
mustang-browser[.]com
forestbrowser[.]com
luckysearch123[.]com
ooxxsearch[.]com
search2000s[.]com
walasearch[.]com
hohosearch[.]com
yessearches[.]com
d3l4qa0kmel7is[.]cloudfront[.]net
d5ou3dytze6uf[.]cloudfront[.]net
d1vh0xkmncek4z[.]cloudfront[.]net
d26r15y2ken1t9[.]cloudfront[.]net
d11eq81k50lwgi[.]cloudfront[.]net
ddyv8sl7ewq1w[.]cloudfront[.]net
d3i1asoswufp5k[.]cloudfront[.]net
dc44qjwal3p07[.]cloudfront[.]net
dv2m1uumnsgtu[.]cloudfront[.]net
d1mxvenloqrqmu[.]cloudfront[.]net
dfrs12kz9qye2[.]cloudfront[.]net
dgkytklfjrqkb[.]cloudfront[.]net
dgkytklfjrqkb[.]cloudfront[.]net/main/trmz[.]exe
File Hashes:
FAB40A7BDE5250A6BC8644F4D6B9C28F
69FFDF99149D19BE7DC1C52F33AAA651
B56D1D35D46630335E03AF9ADD84B488
2579DF066D38A15BE8142954A2633E7F
8C61A6937963507DC87D8BF00385C0BC
7ADB7F56E81456F3B421C01AB19B1900
84DCB96BDD84389D4449F13EAC750986
5BCE955CF12AF3417F055DADC0212920
2B307E28CE531157611825EB0854C15F
7B2868FAA915A7FC6E2D7CC5A965B1E7
66E4D7C44D23ABF72069E745E6B617ED
Countermeasures:
- Do not click on banners or pop-up or ads notifications.
- Check for the default setting of your web browsers, such as the default home page, default search engine, browser extensions and plug-ins installed etc. If found unknown setting then delete the same.
- Monitor the traffic generated from client machines to the domains and IP address mentioned above in Indicator of Compromise (IoC) section.
- In browser, set Internet and Local intranet security zone settings to "High" to block ActiveX Controls and Active Scripting in these zones.
- Refer Desktop security: http://www.cyberswachhtakendra.gov.in/documents/Desktop_security.pdf
- Exercise caution while installing third party applications or freeware software solutions.
- Do not visit untrusted websites.
- Do not download or open attachment in emails received from untrusted sources or unexpectedly received from trusted users.
- Application whitelisting/Strict implementation of Software Restriction Policies (SRP) to block binaries running from %APPDATA%, %PROGRAMDATA% and %TEMP% paths. Malware sample drops and executes generally from these locations.
- Enforce application whitelisting on all endpoint workstations.
- Use limited privilege user on the computer or allow administrative access to systems with special administrative accounts for administrators.
- Enable a personal firewall on workstation.
- Install and scan anti malware engines and keep them up-to-date.
- Keep the operating system third party applications (MS office, browsers, browser Plugins) up-to-date with the latest patches.
- Disable unnecessary services on user workstations and servers, if not in use.
- Maintain situational awareness of the latest threats; implement appropriate ACLs.
References:
- http://blog.checkpoint.com/2017/06/01/fireball-chinese-malware-250-million-infection/
- http://www.digitaljournal.com/tech-and-science/technology/chinese-fireball-malware-could-cause-global-catastrophe/article/494064
- https://www.infosecurity-magazine.com/news/fireball-infects-20-of-corporate/
- http://www.darkreading.com/threat-intelligence/chinese-fireball-malware-infects-20--of-global-corporate-networks/d/d-id/1329025
- http://www.eweek.com/security/fireball-hijack-infects-250-million-browsers-check-point-discovers
- http://www.ibtimes.co.uk/fireball-malware-could-spark-global-catastrophe-after-infecting-250-million-computers-already-1624286
- http://www.quickheal.co.in/bot-removal-tool