ThiefQuest Ransomware
Original Issue Date:- July 20, 2020
Updated on:- July 24, 2020
Virus Type:- Ransomware
Severity:- Medium
It has been reported that a new MacOS ransomware, named “ThiefQuest ransomware” or “EvilQuest ransomware” is spreading since June 2020. This ransomware not only encrypts the files on the system but also installs a keylogger, remote shell and steals cryptocurrency wallet-related files from infected hosts. Even after ransom has been paid by the victim, the attacker continue to have access to the computer and can exfiltrate files and keystrokes. So, the attackers can carry on spying the victims indicating ransomware activity is not its main attack but a pre-emptive attempt to hide its other capabilities.
Infection mechanism:
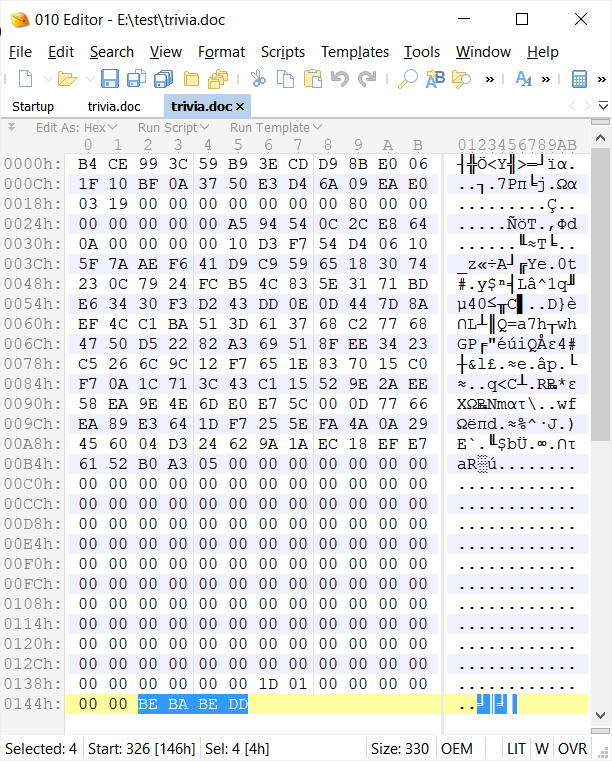
This ransomware is distributed via legitimate applications on torrent websites such as Little Snitch, Ableton, and Mixed in Key. After launching the installer, ThiefQuest starts encrypting files appending a BEBABEDD marker at the end. Ransomware will encrypt any files with the following file extensions:
.pdf, .doc, .jpg, .txt, .pages, .pem, .cer, .crt, .php, .py, .h, .m, .hpp, .cpp, .cs, .pl, .p, .p3, .html, .webarchive, .zip, .xsl, .xslx, .docx, .ppt, .pptx, .keynote, .js, .sqlite3, .wallet, .dat
It has been seen that it limits the number of files to be encrypted to 3000.
When encryption is completed, it creates a text file named READ_ME_NOW.txt with the ransom instructions.
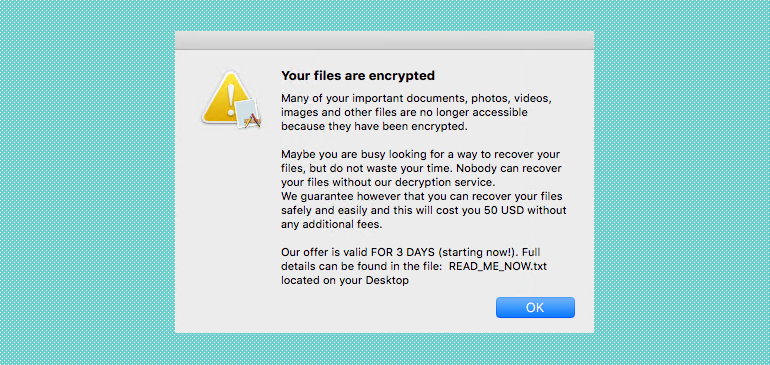
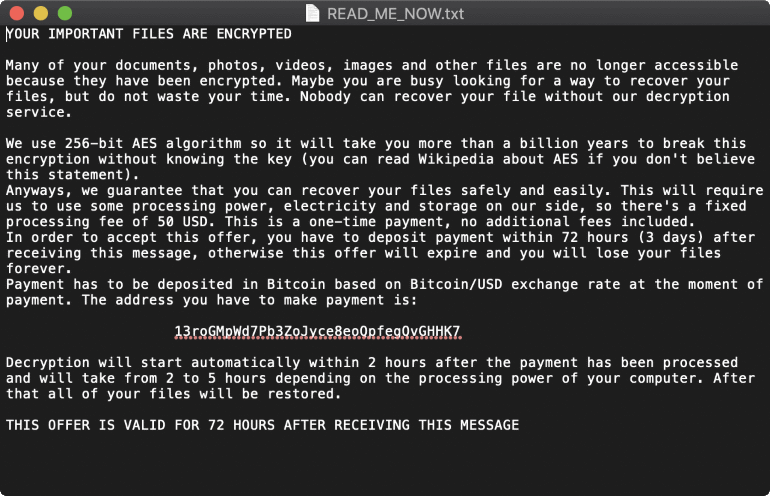
Also, the message in Fig.3 does not contain any email address to contact the hackers for decryptor after the ransom has been paid. This makes it impossible for attackers to identify victims who have paid ransomware. This leads to suspicion that ransomware may be used for spying and other malicious activity.
ThiefQuest downloads Python scripts disguised as GIFs and then run them. If a file matches the search criteria, it will base64 encode the file contents and send it to C&C server. These files include text files, images, Word documents, SSL certificates, code-signing certificates, source code, projects, backups, spreadsheets, presentations, databases, and cryptocurrency wallets.
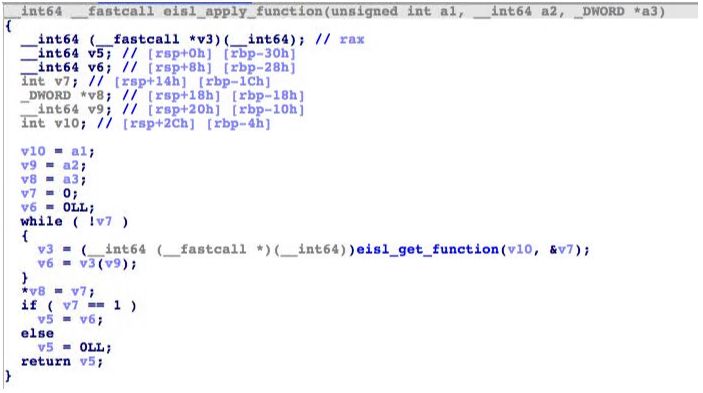
In newer versions, ransomware functionality has been completely removed. Updates are not called by main code but through a new routine for computing and calling new addresses. It first install autorun mechanism to ensure that malware is running on startup. Several functions have been added for anti-analysis, including functions to identify security tools running in the system and terminate them. Run_audio and run_image are new functions that are meant to save a target file into a hidden .m4a sound file or .jpg image file respectively. These functions would be then run through hidden opened terminal with default applications associated with either, such as Music.app or Preview.app. It is possible that in future, ransomware may use text-to-speech functionality to read its dropped ransom note.
Indicators of compromise:
Websites:
- hxxp://andrewka6[d0t]pythonanywhere[d0t]com/ret[d0t]txt
- hxxp://167[d0t]71[d0t]237[d0t]219
- http://lemareste[d0t]pythonanywhere[d0t]com/cfgr[d0t]txt
File locations:
- /var/root/.aespot
- ~/.aespot
- ~/Library/LaunchAgents/com.apple.abtpd.plist
- ~/Library/PrivateSync/com.abtpd.questd
- ~/Library/LaunchDaemons/com.apple.abtpd.plist
- ~/Library/PrivateSync/com.abtpd.questd
Hashes:
- 06974e23a3bf303f75c754156f36f57b960f0df79a38407dfdef9a1c55bf8bff
- d18daea336889f5d7c8bd16a4d6358ddb315766fa21751db7d41f0839081aee2
- c5a77de3f55cacc3dc412e2325637ca7a2c36b1f4d75324be8833465fd1383d3
- effeeeadfdc3caf523635fcb86581a807f719fa5e322872854499f5270bc0eba
- 365a5c72f52de964b8dc134d2fc45f9c73ba045cebd9fd397b1e26fdb11bfec6
- eeac57f7ca9df9199f0346ed9097e9f5482c06214cddc162d1500d15d045b4ed
- 5a024ffabefa6082031dccdb1e74a7fec9f60f257cd0b1ab0f698ba2a5baca6b
- e69e9dc0d343165aa0f5df942d1b48ddd0337c8a79dcdf40f3c3b490d6e96a78
- f7efda39c80d68db168316732732d04a00fe6fb10f37d1013df1a8a4cde1f68a
- 851dfdbffd250523c5c7ff07b29778a04ebd44400b12f23d18a6ee5a3fcfbedc
- 41036e1b78a122e57f2125526d673ffe3358d7323fc577703662740b3e651dcc
- 7292004b57562223fed4ee122a956a8db38349c95d4dd8853b1ebc60ef7508b1
- 92ad2b0220f6903fb5fa48ce411af44a60c06031fee3aa682bd28f3f3fde1eda
- bcdb0ca7c51e9de4cf6c5c346fd28a4ed28e692319177c8a94c86dc676ee8e48
Countermeasures and Best practices for prevention:
- Users are advised to disable their RDP if not in use, if required, it should be placed behind the firewall and users are to bind with proper policies while using the RDP.
- All operating systems and applications should be kept updated on a regular basis. Virtual patching can be considered for protecting legacy systems and networks. This measure hinders cybercriminals from gaining easy access to any system through vulnerabilities in outdated applications and software. Avoid applying updates / patches available in any unofficial channel.
- Restrict execution of Power shell /WSCRIPT in an enterprise environment. Ensure installation and use of the latest version of PowerShell, with enhanced logging enabled. Script block logging and transcription enabled. Send the associated logs to a centralized log repository for monitoring and analysis.
https://www.fireeye.com/blog/threat-research/2016/02/greater_visibilityt.html - Establish a Sender Policy Framework (SPF) for your domain, which is an email validation system designed to prevent spam by detecting email spoofing by which most of the ransomware samples successfully reaches the corporate email boxes.
- Application whitelisting/Strict implementation of Software Restriction Policies (SRP) to block binaries running from %APPDATA% and %TEMP% paths. Ransomware sample drops and executes generally from these locations.
- Don't open attachments in unsolicited e-mails, even if they come from people in your contact list, and never click on a URL contained in an unsolicited e-mail, even if the link seems benign. In cases of genuine URLs close out the e-mail and go to the organization’s website directly through browser.
- Block the attachments of file types, exe|pif|tmp|url|vb|vbe|scr|reg|cer|pst|cmd|com|bat|dll|dat|hlp|hta|js|wsf
- Consider encrypting the confidential data as the ransomware generally targets common file types.
- Perform regular backups of all critical information to limit the impact of data or system loss and to help expedite the recovery process. Ideally, this data should be kept on a separate device, and backups should be stored offline.
- Network segmentation and segregation into security zones - help protect sensitive information and critical services. Separate administrative network from business processes with physical controls and Virtual Local Area Networks.
- Install ad blockers to combat exploit kits such as Fallout that are distributed via malicious advertising.
References:
- https://www.bleepingcomputer.com/news/security/thiefquest-ransomware-is-a-file-stealing-mac-wiper-in-disguise/
- https://www.zdnet.com/article/new-evilquest-ransomware-discovered-targeting-macos-users/
- https://www.zdnet.com/article/free-decryptor-available-for-thiefquest-ransomware-victims/
- https://www.sentinelone.com/blog/evilquest-a-new-macos-malware-rolls-ransomware-spyware-and-data-theft-into-one/
- https://blog.trendmicro.com/trendlabs-security-intelligence/updates-on-thiefquest-the-quickly-evolving-macos-malware/